A recent announcement by AWS may have been missed by many users as it was made at the beginning of the year. AWS now encrypts all new buckets and (new) objects (in those buckets) by default. This new default does not change any pre-existing buckets or data in those pre-existing buckets, it only applies to new buckets and new data in the new buckets.
Whereas previously you could, very quickly and easily, enable encryption, it was an opt-in choice, and it meant that users had to check that this had been selected and that it hadn’t been changed since it was implemented.
AWS now automatically applies Server-Side Encryption (SSE-S3) for all new objects unless you specify no encryption or another encryption option (options include SSE-KMS and SSE-C). Below you can see the default setting on a new bucket:
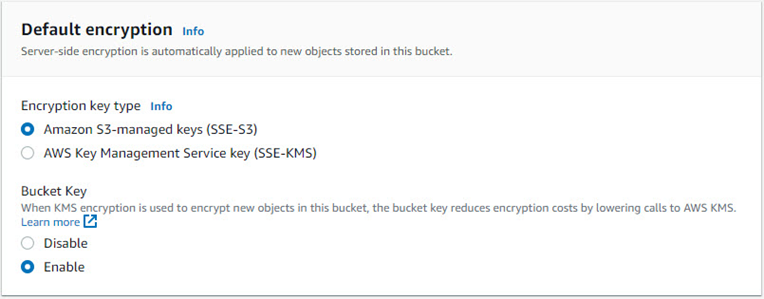
This new default does help organisations meet with their encryption compliance requirements without requiring additional configurations or tools.
BUT, and this is vitally important, enabling encryption DOES NOT block unauthorised users from accessing your data…
This is important to understand as the AWS default key policy (the default permissions to access the encryption/decryption key) for S3 is to allow access for anyone or anything authorised to access the data. (See the default policy image below).
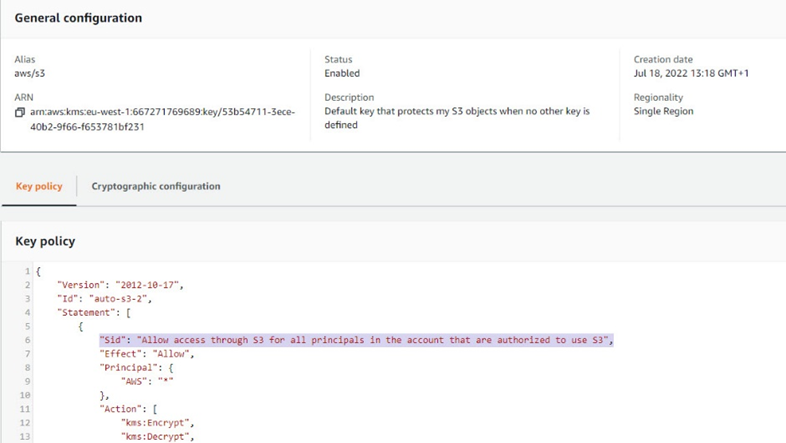
So in a nutshell, IF you allow someone (or something) to access your data, you are also allowing the data to be decrypted on access, which seems obvious in hindsight.
If you need to know how to better protect your encrypted data – engage with us or join one of our many AWS training courses. Our public scheduled course list is available here:- https://www.sureskills.com/Courses/Vendors/AWS-Amazon-Web-Services/
Ref:
https://aws.amazon.com/blogs/aws/amazon-s3-encrypts-new-objects-by-default/