In the first part of this article, I looked at some of the challenges that GDPR presents for many organisations. Among them is the need to demonstrate compliance, which requires being able to understand where all of an organisation’s data resides. Responding to subject access requests can be extremely time-consuming, which in turn can eat into the productivity of senior staff and prove to be a costly exercise.
This is where technology can come into play. Enter Commvault Activate.
Typically, we are seeing organisations taking up to 3 weeks to address SARs depending on how extensive the request is, or the nature of the request. SARs really rely of two things – having a handle on where every record is (and what it relates to), and being able to guarantee that the request has been completely addressed. A DPIA and data categorisation exercise should address the first part, but even then there is the risk that new data has entered the environment since the DPIA was carried out. And there is always the risk of human error playing a factor. All of this makes for a costly exercise – not only is a fee-earner or employee spending nearly a month addressing SARs, they are not fulfilling the tasks they were employed for. So what can technology do?
Commvault is already well established in the Enterprise Backup space, ranked as a leader in Gartner’s Magic Quadrant for Data Centre Backup and Recovery Solutions over the last decade.
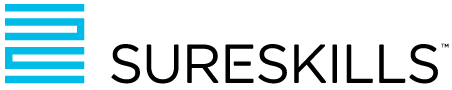
Continuing the trend of delivering innovation, Commvault launched Activate in 2018 to make an organisation’s protected data available in a similar fashion to a data lake. This extended the ability of the existing CommVault product to be able to index and search structured and unstructured data repositories, either within the backup data set, or using agents to connect to databases, email, file servers and even client devices. This eDiscovery functionality is coupled with a highly distributed indexing and searching configuration that enables CommVault to index simultaneously on multiple servers and search across these search servers.
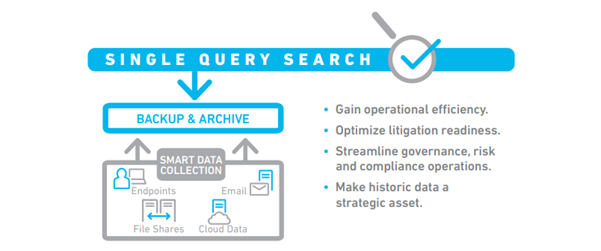
Coupled with Commvault’s powerful 4D Index, this makes for a tool which provides you with not just the ability to search all manner of data sources, but also to understand the context they have within your organisations data landscape.
Commvault Activate uses this 4D Index to search, discover and learn about different types of data, the data context and relationship within the organisation. The search queries can be pointed at your backup sets, thereby negating any impact on production infrastructure, or live production data.
|
At a basic level, this Commvault Activate can be used to answer some fundamental questions, such as: • How many copies of my data exist? • Where are they? • Who has access to the data? |
Meeting the GDPR challenge
If we extend these capabilities into the realm of GDPR, Activate takes on a whle new meaning for an organisation. Activate is not only indexing all data across the organisation, but also allows for advanced searches viewed through the privacy lens.
Activate will index and analyse data across multiple data silos, including the full text of emails and files contained within backups, archives or directly from other data sources. This information is fully searchable, and the tool allows for action-oriented decision making. Using open APIs, you can connect to specialised third-party data services. One fo the interesting features of Activate is the ability to run a sentiment search. This looks for tone within text.
Optimising compliance activities
Activate’s Sensitive Data Governance (SDG) accelerator, can greatly reduce risk and optimise your compliance activities. SDG can detect and extract sensitive data from within file content, based on a prebuilt set of personally identifiable information (PII) data profiles (according to regulations such as GDPR or HIPAA, for example).
Proactive privacy
Information risk reports and other visualisations show where information resides, which allows you to focus on the most critical items first and build your remediation and protection priorities from there. You can proactively remediate data privacy risks before they become a problem or respond to data subject requests with review and approval workflows. Pre-built reports show you access history to indicate inactive or critical files. Reports will highlight pockets of sensitive data that might require protective actions or show organisational ownership and distribution of files to drive more accountability and decision making.
Supporting eDiscovery
Activate will also support investigations and eDiscovery requests by allowing you to search for relevant content across emails and file shares, assemble collections of content for further use and export records to be used with external systems and service providers.
Activate works across structured and unstructured data, which makes this particularly powerful in the context of GDPR. Throughout the text of the regulation, there are references to the ability of an organisation to demonstrate compliance. Article 5 lays out how personal data should be treated. It should be processed lawfully, fairly and transparently; collected for explicit and legitimate purposes, limited to what is necessary for said purposes, accurate and kept up to date, personally identifiable only as long as necessary, and secure. By using a tool such as CommVault Activate an organisation can be assured that in the event of a SAR every relevant record has either been captured, exported, corrected or deleted in accordance with the request. Furthermore, the resource burden will have been reduced from weeks to hours, or minutes depending on the nature of the request. When calculated in work hours the cost saving can be significant. Apart from the costs savings there is the assurance that an organisation now has a single pane of glass for all data – where it is located, how often it is accessed and by whom, and whether that data holds and risk in terms of GDPR, HIPAA etc.